These past few days I decided to take a look at perhaps my weakest topic in computer science: Computer Architecture. There is something about these abstract concepts that I have struggled to wrap my head around in the past. So once and for all, I will delve into some of the basics of computer architecture that I covered.
Note: I am aware that this is an oversimplification of these topics. I am just providing a very basic overview that helps build a base since that is what I was struggling with.
User and Hardware
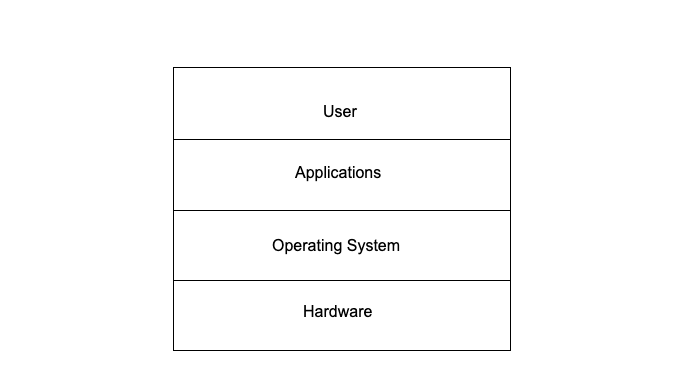
Computer architecture, similar to a range of other topics in computer science, is a very hierarchical subject. Therefore, I think it is best to approach this from a top-down perspective, and then work our way down. To begin with, it is important to understand, at a very basic level, the relationship between the user interacting with a computer and its hardware components. Hardware encompasses the physical machines and devices on and including the motherboard. On top of the hardware layer, we have the operating system.
Operating System & Kernel
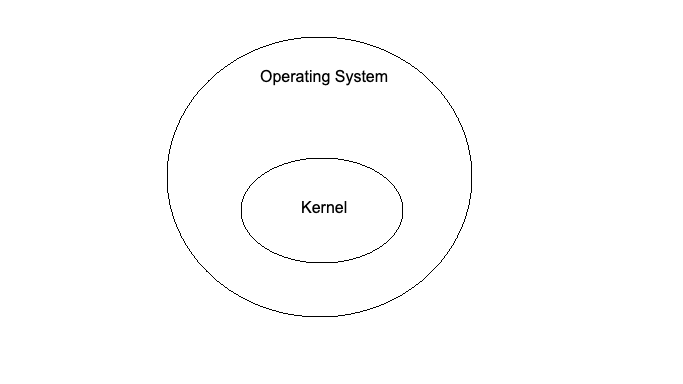
The operating system is software manages the computer’s software and hardware and acts as a translator between the user and hardware. At the very core of an operating system we have something called the ‘kernel’. The kernel has complete control over everything in the system. The kernel layer includes device drivers, which are files that allow the operating system to talk to the hardware. This bridges the gap between the hardware components and the operating system. Recently there has been a surge in BYOVD (Bring Your Own Vulnerable Driver) attacks. These are incredibly powerful given that the exploitation takes place at the kernel layer, and as we mentioned earlier, the kernel has complete control over the system.
There are three operating systems that currently dominate the market. The most popular of these is Windows. The Windows operating system is based on DOS. The story behind this harkens back to when IBM were designing their first PC. They required an operating system so they asked Microsoft for help. Microsoft hired a man called Tim Paterson who created DOS, and bought it from him. Then Microsoft renamed the operating system to MS-DOS and sold IBM a license. Eventually, the name of the operating system was changed to Windows.
The Windows operating system family is very different to macOS and Linux which come from the Unix operating system… Sort of.
Unix is an operating system that was created by a group of computer scientists that were working on an operating system called Multix. Disillusioned with the unnecessary complexity of Multix, they eventually created the Unix operating system. Unix nowadays is an umbrella term that encompasses any operating system that behaves like a Unix operating system (according to certain criteria). MacOS is based on FreeBSD and BSD, which is based on Unix, making macOS a Unix operating system. Linux however is not a descendant of Unix, but it is referred to as a Unix-like operating system due to its similar characteristics.
Memory and Storage
Looking now at a layer below the operating system, we have the computer’s hardware. In this section, we will briefly cover memory and storage.
Memory refers to what is stored in Random Access Memory (RAM) and storage refers to what is stored in the HDD (hard disk drive).
Note: This is not entirely correct since space in the disk can be used as (swap) memory. We will cover that in the next section.
RAM is volatile, meaning that data in memory is erased when the computer is powered off. A HDD is non-volatile, which means that data stored on the disk is not erased when the computer is powered off.
Virtual Memory
Data in RAM is very unorganised and programs can interfere with each other. Therefore, virtual memory was created to allocate dedicated space in memory to programs to avoid this problem.
When talking about virtual memory, I love to use the analogy of the table and the bookshelf. The table represents RAM and the bookshelf represents the HDD. When you want to use something, you go to the bookshelf (HDD), grab a book (a program), and put it on the table (RAM). Soon, you end up with a lot of books on the table and it becomes very unorganised. I conceptualise virtual memory as a hologram of the table above the table. This holographic table however is very tidy and organised; all the books you are using for a specific project are on one side of the holographic table for example. These virtual memory address spaces that the programs occupy (on our holographic table) are mapped to physical addresses (on our actual table).
If our table (RAM) is completely full, we can use something called “swap memory”. Swap memory is a type of virtual memory. It simply refers to when storage space in the HDD is used as extra RAM. However, this makes that data a lot slower to access.
Booting
Finally, we will take a look at a typical booting process for a PC. We need to begin by understanding a couple more things.
On a small chip on the motherboard, we have a piece of firmware called the BIOS (Basic Input Output System). Simply put, firmware is software for hardware. The BIOS plays a pivotal role in the booting process as it is responsible for loading the operating system into RAM. Nowadays however, the BIOS has been replaced with a more modern firmware called UEFI (Unified Extensible Firmware Interface). We will cover this in more detail when explaining the booting process.
Another important detail to understand is how a hard disk drive is structured. In our HDD, we have a primary partition which is where the operating system is stored. The secondary partition is where all other data such as files is stored. Multiple primary partitions can be created. There are usually two primary partitions in a hard disk drive. One is called the GPT (GUID Partition Table) partition which is where the “bootloader” is stored – firmware that is responsible for booting a computer. Then the other primary partition stores the host operating system.
Typically when booting is explained, the MBR (Master Boot Record) partition is brought up. MBR is the antiquated version of GPT, similar to how BIOS is the antiquated version of UEFI. MBR is a type of boot sector at the beginning of the hard disk drive that contains information on how the disk is partitioned as well as code that can load the operating system into RAM.
A typical boot sequence goes as follows:
1. The CPU talks to the BIOS and tells it to begin the booting process.
2. The BIOS runs a POST (Power-On Self-Test) to initialise hardware.
3. The BIOS loads the MBR/GPT into RAM.
4. The BIOS runs the MBR/GPT code that loads the OS into RAM.
5. The OS initialises itself and loads device drivers, finalising the link between the hardware and the OS. From here on out, any data from the hard disk drive is moved into RAM by the OS.
Conclusion
My notes for this post were quite untidy and I became very complacent trying to organise it, but I have finally finished and written it to a reasonable standard I hope. I learnt a lot reading about all of these topics. And it all stemmed from going down a rabbit-hole after reading the title of an article about the LogoFAIL vulnerability!